How to Configure a Netgate pfSense Firewall for 8x8 Service
The purpose of this article is to provide a sample configuration. At the time of article creation, this device was in a known working state on the firmware used.
Keep in mind different firmware versions will interact with hosted VoIP services in different ways. While this device may be fully functional on the tested and/or current firmware version, it is possible newer revisions will cause disruptions in service or make a device fully compliant with the required settings for hosted VoIP services where it was previously not.
General Information
Note: Guidance on pfSense firewall is publicly available within pfSense documentation.
Administrative Information
- In a browser on a computer on the same network as the pfSense firewall, navigate to your pfSense IP address you have assigned to it.
- Log in (default credentials shown below).
- Username: admin
- Password: pfsense
Tested on the following firmware versions:
-
Fimware version 2.4.3 and later
Adding/editing 8x8 subnets is recommended when available. Please click here and review the Traffic Shaping and Specific Subnet/Port Configuration section.
Procedure
Set Conservative state table optimization
- Go to System > Advanced
- Click Firewall & NAT
- Set ‘Firewall Optimization Options’ to Conservative
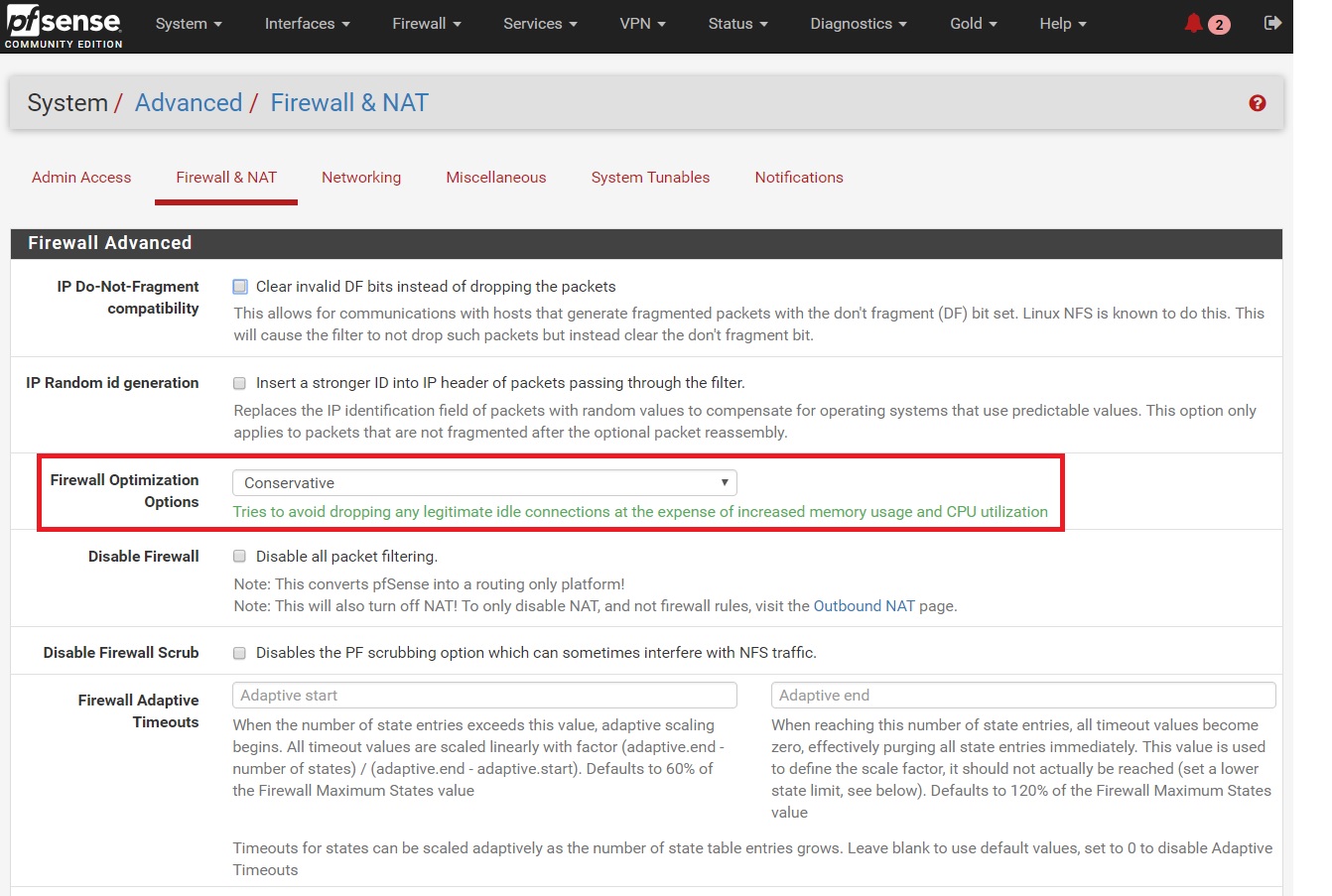
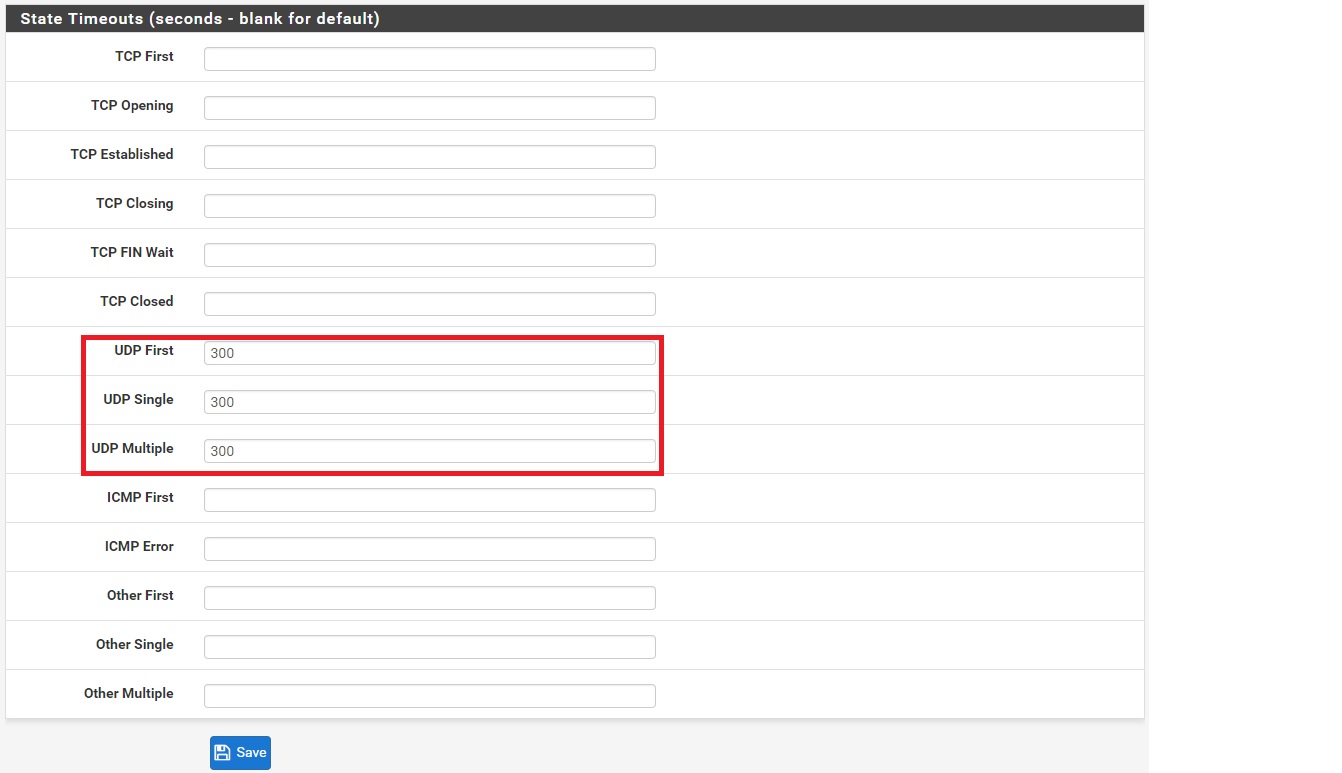
- Under the ‘State Timeouts’ section set ‘UDP First, Single, and Multiple’ to 660
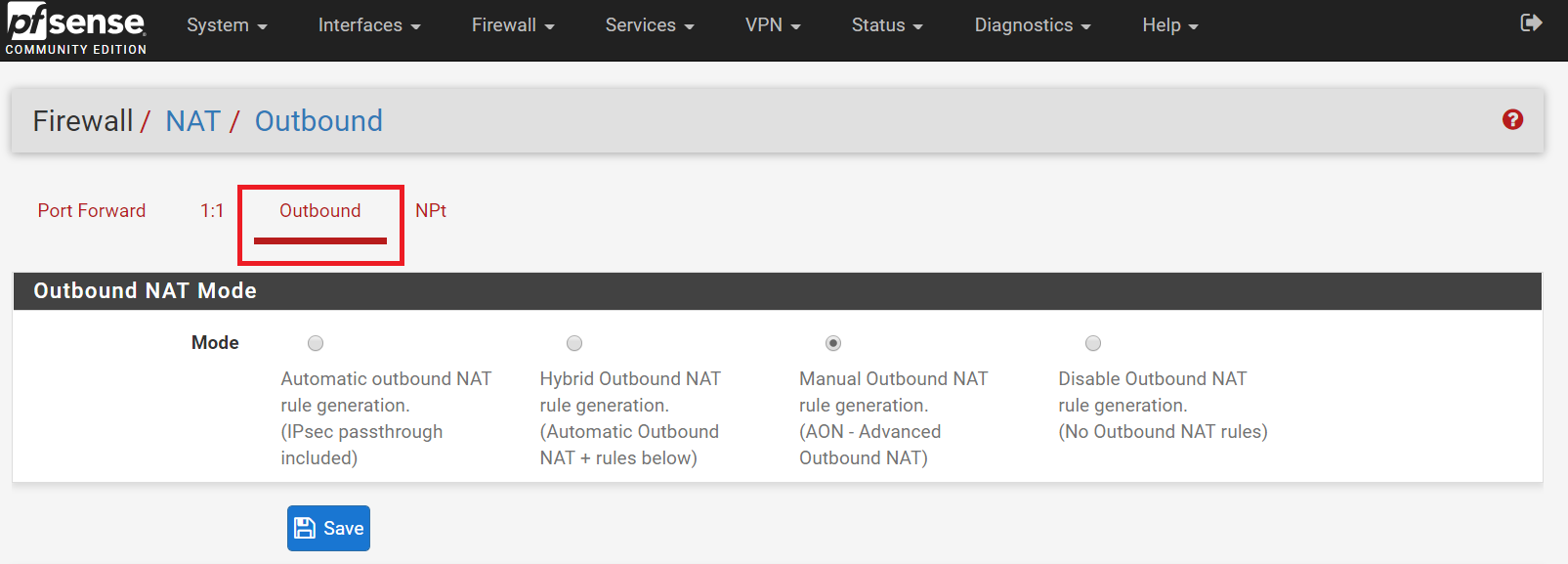
Set up Outbound NAT
- Go to Firewall > NAT
- Click Outbound
- Set ‘Outbound Nat Mode’ to Manual Outbound NAT rule generation (AON - Advanced Outbound NAT)
Add 8x8 Subnets
- Go to Firewall > Rules
- Click LAN
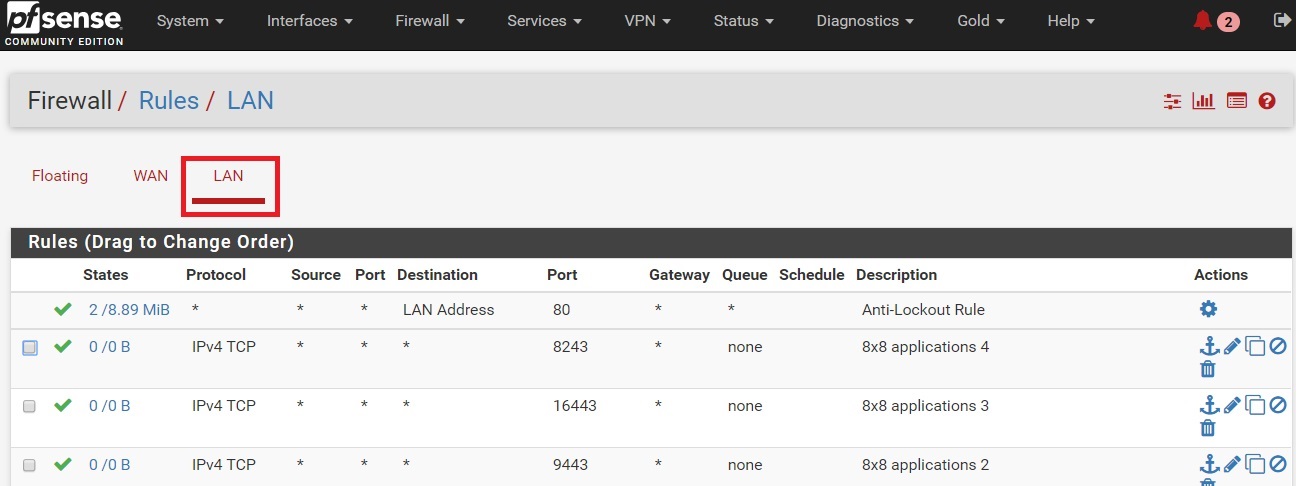
- Click Add
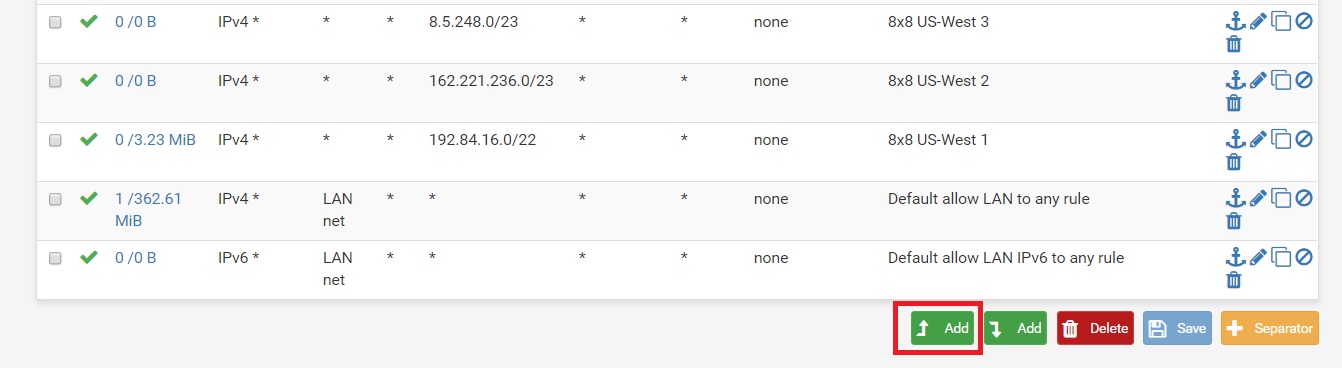
- Add each 8x8 subnet one at a time. (One example shown. For the full subnet list, see 8x8 Work Technical Requirements.)
- Add each 8x8 ports one at a time. (For the full port list, see 8x8 Work Technical Requirements.)
Set up Traffic Shaping
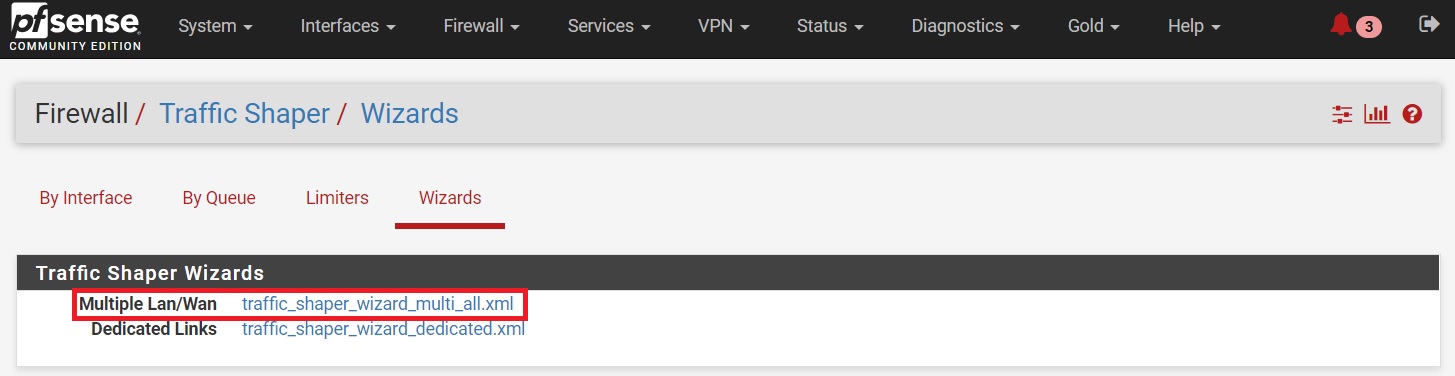
- Go to Firewall > Traffic Shaper.
- Click Wizards.
- Click Multiple Lan/Wan.
- Enter the number of Wan type connections and LAN type interfaces.
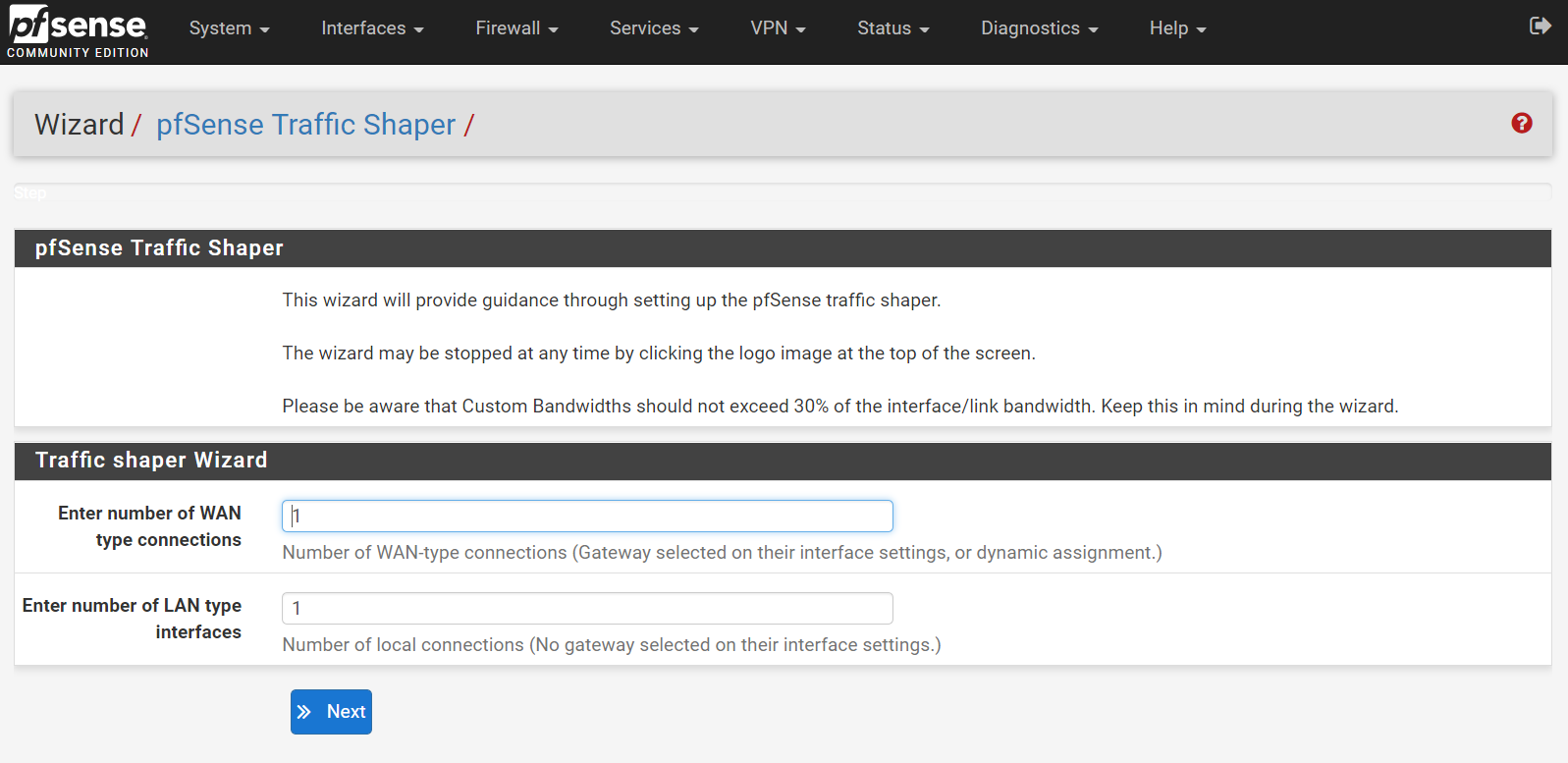
- Select HFSC for ‘Interface & Scheduler.’
- Make sure your Upload and Download speed is set correctly, if you have an internet connection established on your pfSense, it should be set automatically. Enter your interface WAN#1 upload and download speed. (Screenshot below is an example, every network will have different up/down speed, we highly recommend working with your IT department or system administrator for the correct up/down speed for your network.)
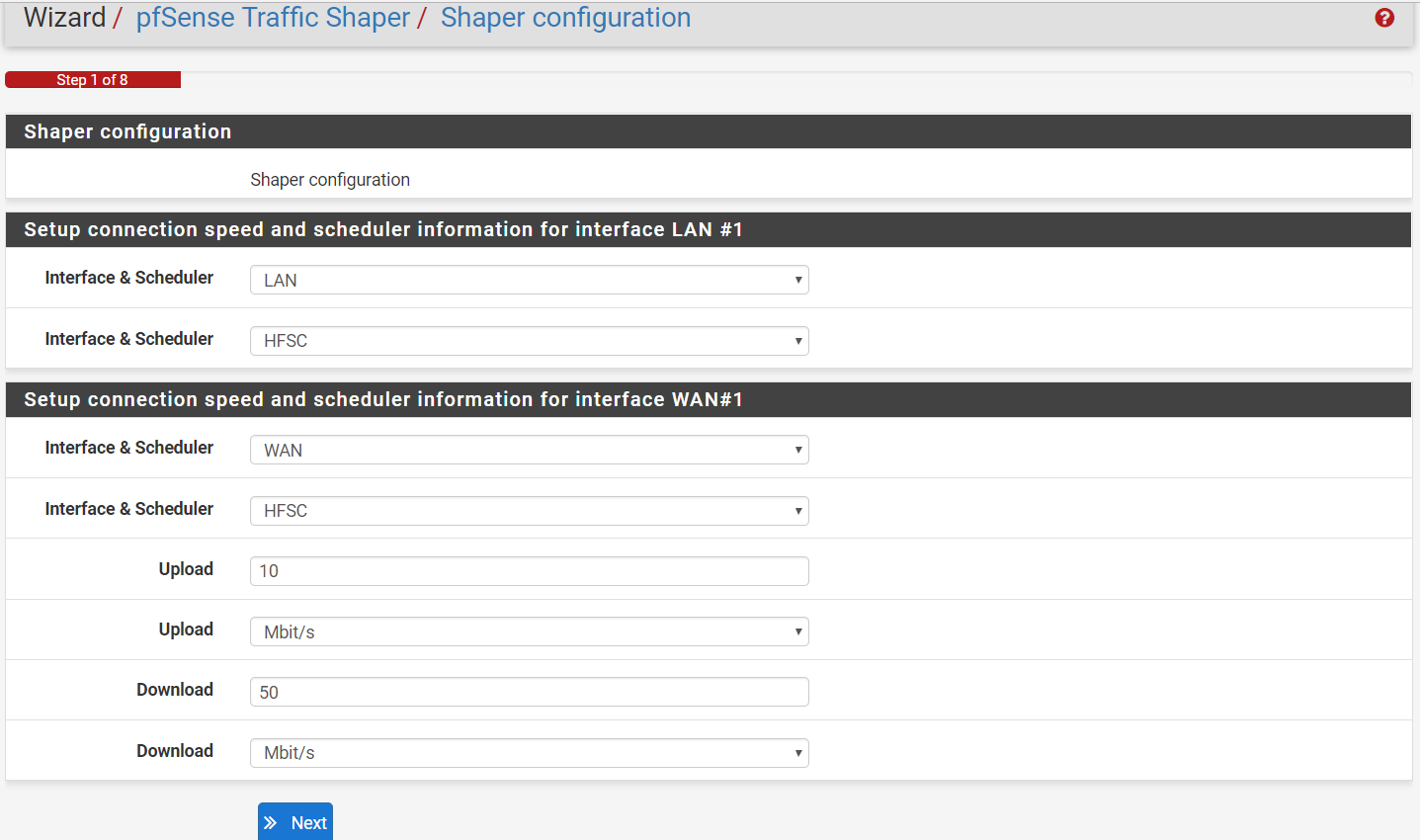
- Click Next.
- Under the ‘Voice over IP’ section Enable Prioritize Voice over IP traffic.
- The next Step really depends on how many users you have on your network. In this example, the network is highly unlikely that more than 5 people will have a phone call at the same time. In this step we are going to set bandwidth we want to reserve for our VOIP traffic, in this example we set the ‘Connection for WAN#1 and LAN#1’ limits to 1Mbit/s Up/Down.
As a rule of thumb you can assume the following traffic rules:
|
Number of Concurrent Calls |
Minimum Required Bandwidth |
Recommended Speed |
|
1 |
100 Kbps Up and Down |
3 MBps Up and Down |
|
3 |
300 Kbps Up and Down |
3 MBps Up and Down |
|
5 |
500 Kbps Up and Down |
5 MBps Up and Down |
|
10 |
1 MBps Up and Down |
5-10 MBps Up and Down |
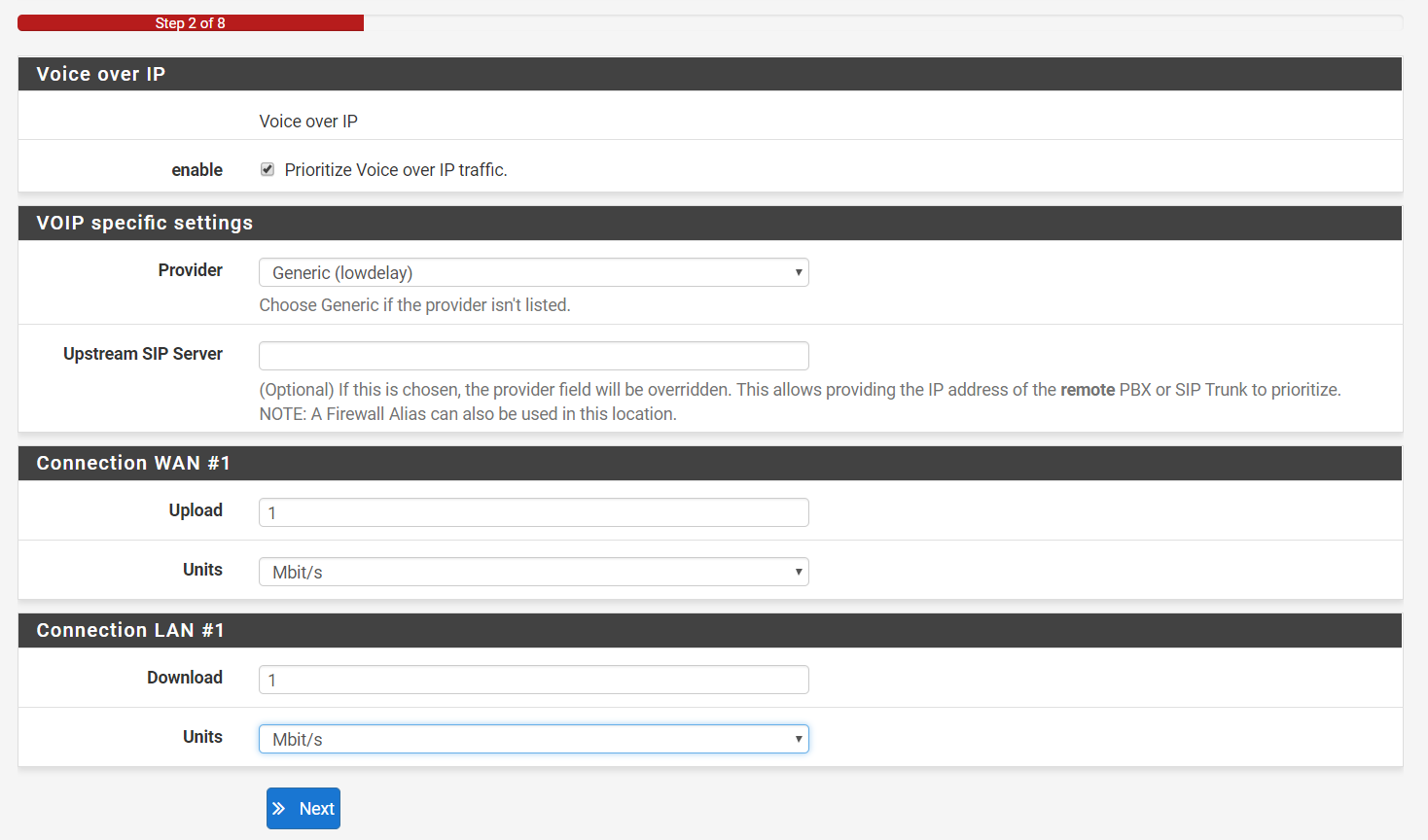
- Click Next.
- The next steps are unique to each network, make sure you go through each section and check anything that pertains to your network until the get to the end of the Wizard.
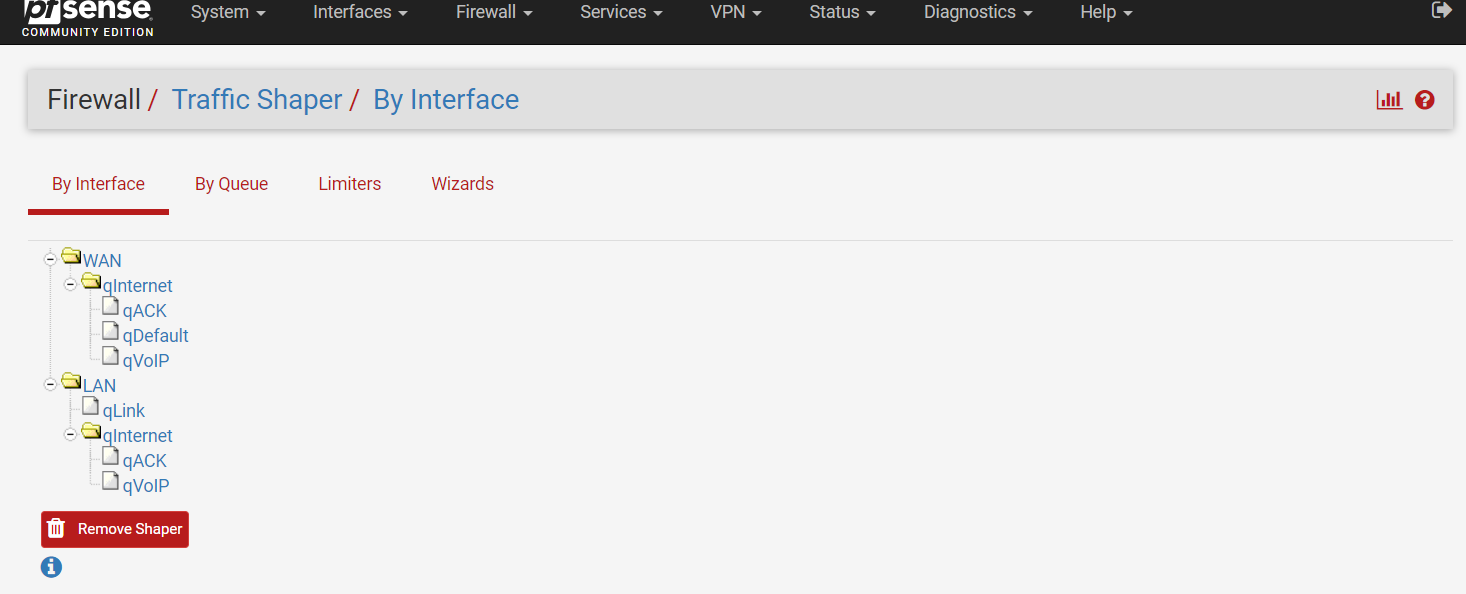
- Confirm the wizard has created the proper queues for your network by navigating back to Firewall > Traffic Shaper.
- Click By Interface.
- In this section, you can modify or adjust the queues that were created by the Wizard. Note, this is the fastest and easiest way of creating the Traffic Shaping rules, there are multiple ways of creating these queues. You can find more information on creating these rules by visiting the pfSense website and forums.